
GSA Sales in 2018,IT Schedule

Contractors

Average Sales per Contractor
The Information Technology category of the MAS (GSA Schedule) Program offers IT Services, Hardware, Software, and a variety of specialty IT offerings. Previously known as IT Schedule 70, this is one of the largest government contracts.For decades, The GSA’s IT Schedule 70 has been the largest moneymaker for the GSA. Consistently, Schedule 70 accounts for about half of the sales going through the GSA Contract program (all 33 GSA Schedules).IT Schedule 70 is a Multiple Award Schedule (MAS) contract under the GSA Schedule Program. The type of contract is called an Indefinite Delivery Indefinite Quantity (IDIQ), which means that there are no orders or dollars attached to the award, but it is rather a channel for sales to flow through (i.e. a License to hunt). It is the major procurement vehicle for IT products, software and Professional Services.
Contractors that sell IT products, software, and Professional Services, may want to consider pursuing the GSA IT Schedule 70 Contract to grow or develop their Federal Business prospects. GSA Schedule 70 is the largest within the GSA Schedules Program both by sales and the competition. The average amount of revenue of a GSA Schedule 70 Contractor is about $3.1 million per year.
Primarily, the Schedule 70 Contract is used to sell to federal buyers. However, State, Municipal and Local government agencies can purchase through the Cooperative Purchasing and Disaster Recovery programs. That being said, the federal government mainly uses The GSA IT Schedule 70 as a major source for simplified IT purchases. Federal buyers enjoy the value that IT Schedule 70 purchases bring in saving time and money.
GSA Schedule 70 Has 4 basic categories of Special Item Numbers (SIN’s).

(Previously SIN 132-51)
Information Technology Professional Services includes resources and facilities management, database planning and design, systems analysis and design, network services, programming, conversion and implementation support, network services project management, data/records management, and other services.Sub-Categories for SIN 5415S include:Auto. Info. System Design & Integration, Automated News, Data and other Info. Services, CAD/CAM Services, Desktop Management, IT Backup and Security Services, IT Data Conversion Services, IT Facility Operation and Maintenance, IT Network Management Services, IT Systems Analysis Services, IT Systems Development Services, Information Assurance, Programming Services.

(Previously SIN 's 132-8 & 132-9)
Purchase of New IT Equipment (33411) and Refurbished Equipment (33411REF) is available under Schedule 70. There are many categories of IT Products that federal buyers can purchase through these SINs:Boards, Cables, Desktop Computers, Digital Cameras, Display, Monitors, Drives/Storage Devices, Equipment for Physically Challenged, IT Support Equipment, Laptop/Portable/Notebook Computers, Large Scale/Mainframe Computers, Media, Memory, Microcomputer Control Devices, Modems, Graphic Related Equipment, MP3 Devices, Networking, Optical Imaging Systems, Optical Recognition I/O Devices, Other Communications Equipment, Other I/O and Storage Devices, PDAs, Power Protect, Printers, Professional Workstations, Projectors, Scanners, Servers, Speakers, Used Equipment, Video Cards, Web Cams, Airborne Radar Equipment, Broadcast Band Radio, Microwave Radio Equipment, Radio Navigation Equipment/Antennas, Radio Transmitters/Receivers, Airborne, Satellite Communications Equipment, Two-Way Radio, Telephone Equipment, Audio and Video Teleconferencing Equipment, Communications Security Equipment, Facsimile Equipment, Telephone Answering and Voice Messaging, Pagers and Public Address Systems, Misc. Communication Equipment.

(Previously SIN 's 132-32, 132-33 & 132-34)
Term & Perpetual Software Licenses (SIN 511210) and Maintenance of Software as a Service (54151) make up the software SINs for Schedule 70. A large variety of Software applications are offered under these SINs, including:Operating system software, application software, EDI translation, and mapping software, enabled E-mail message based products, Internet software, database management programs, and other software. Software maintenance as a product includes the publishing of bug/defect fixes via patches and updates/upgrades in function and technology to maintain the operability and usability of the software product. It may also include other no charge support that is included in the purchase price of the product in the commercial marketplace. No charge support includes items such as user blogs, discussion forums, on-line help libraries and FAQs (Frequently Asked Questions), hosted chat rooms, and limited telephone, email and/or web-based general technical support for users self-diagnostics. SubSIN categories include Ancillary Financial Systems Software, Application Software, Communications Software, Core Financial Management Software, Electronic Commerce (EC) Software, Large Scale Computers, Microcomputers, Operating System Software, Special Physical, Visual, Speech, and Hearing Aid Software. Provide specific information and Utility Software. Software maintenance as a product does NOT include the creation, design, implementation, integration, etc. of a software package.

Highly Adaptive Cybersecurity Services (HACS) - Includes a wide range of fields such as, the seven-step Risk Management Framework services, information assurance, virus detection, network management, situational awareness and incident response, secure web hosting, and backup, security services and,Security Operations Center (SOC) services. HACS vendors are cataloged under the 5 subcategories of High Value Asset Assessments; Risk and Vulnerability Assessments, Cyber Hunt, Incident Response, and Penetration Testing.
CYBER SINs (54151HACS) / Highly Adaptive Cybersecurity Services (HACS)
Penetration Testing is security testing in which assessors mimic real-world attacks to identify methods for circumventing the security features of an application, system, or network.
Incident Response services help organizations impacted by a Cybersecurity compromise determine the extent of the incident, remove the adversary from their systems, and restore their networks to a more secure state.
Cyber Hunt activities are responses to a crisis or urgent situations within the pertinent domain to mitigate immediate and potential threats.
Risk and Vulnerability Assessments (RVA) conduct assessments of threats and vulnerabilities, determine deviations from acceptable configurations, enterprise or local policy, assesses the level of risk, and develops and/or recommends appropriate mitigation countermeasures in operational and non-operational situations.
SPECIALTY SERVICES SINs
Cloud Computing Services (518210C) includes commercially available cloud computing services such as Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS) and emerging cloud services.
Health Information Technology Services (54151HEAL) includes a wide range of Health IT services to include connected health, electronic health records, health information exchanges, health analytics, personal health information management, innovative Health IT solutions, health informatics, emerging Health IT research and other Health IT services.
Training Courses (611420) offers Information Technology training courses covering a multitude of training topics.
Electronic Commerce and Subscription Services (54151ECOM) includes value added network services, e-mail services, Internet access services, electronic subscription services, data transmission services, and emerging electronic commerce technologies.
Wireless Services (517312) includes, but is not limited to, Wireless Telecommunications Carriers and Telecommunication Resellers.
Earth Observation Solutions (541370GEO) provides geospatial earth observation technologies, products, and services.
Continuous Diagnostics and Mitigation Tools (541519CDM) includes Continuous Diagnostics and Mitigation (CDM) Approved Products List (APL) hardware and software products/tools and associated services.
COMSATCOM Services (517410) includes satellite services used in a multitude of applications.
Identity, Credential and Access Management (ICAM) (541519ICAM, 541519PKI, 541519PIV).
In case you are wondering the spending distribution in GSA Schedule 70, here is a chart and information to show you how much Federal spending went to each major Schedule 70 SIN in 2017:
Professional Services (SIN 132-51): $7 Billion (49.9%)
Software (SINs 132-32, 33, 34): $4.2 Billion (29.8%
Hardware (SINs 132-8, 9): $960.2 Million (6.8%)
All Other SINs: $1.9 Billion (13.5%)
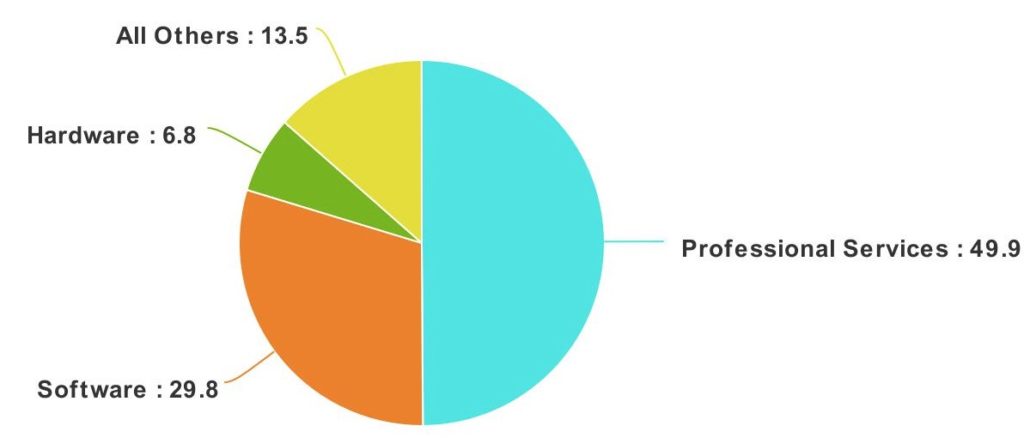
GSA Schedule 70 Spending in 2017: Source: GSA Schedule Sales Query
Buying IT from GSA’s Multiple Award Schedule is easy, because the work is done for you. We offer streamlined procurement options for a full scope of IT supplies and services:
• Negotiated contract ceiling prices
• Opportunities for discounts at the order level
• Single contracting vehicle to fulfill complex or ongoing needs and reduce overall contract awards and administration
• Less administrative time and contract documentation, since the master contract is managed by GSA
• Socioeconomic credit for orders awarded to small business and other socioeconomic categories
Getting a GSA Schedule 70 contract is a very technical process. Each stage requires experience and careful thought in order to result in the best terms, conditions and discount structure being awarded to your Company.
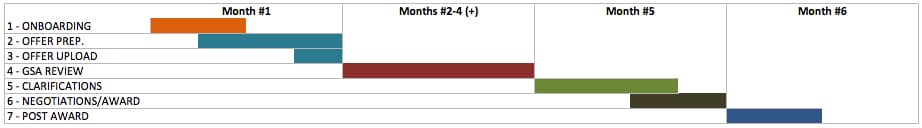
Stages to Get a GSA Contract
Here are the 4 stages:

There are several ways that a federal buyer can purchase through Schedule 70: GSA eBuy, GSA Advantage!, a Direct Purchase, or GSA’s Reverse Auction. However, there are some programs that offer GSA Schedule 70 products and services to State and Municipal Agencies.
The Cooperative Purchasing Program, allows state, local and tribal governments to purchase from vendors offering a variety of information technology products and services (offered through GSA Schedule 70) as well as security and law enforcement products and services (offered through GSA Schedule 84). These entities, like their federal counterparts, can utilize GSAAdvantage!, GSA eBuy and the GSA ReverseAuctions platform under Cooperative Purchasing.
Schedule 70 features a wide variety of information technology products and services including mobile device and mobile application management (MDM/MAM) tools, automated data processing equipment (firmware), software, cloud computing services, hardware, support equipment and related professional services.
From the purchasing side, the term “state and local government” has been meticulously defined for state and local entities. The General Services Administration Acquisition Manual (GSAM), Part 538.7001, Definitions, offers the following definition of state and local governments:
“The States of the United States, counties, municipalities, cities, towns, townships, tribal governments, public authorities (including public or Indian housing agencies under the United States Housing Act of 1937), school districts, colleges, and other institutions of higher education, council of governments incorporated or not), regional or interstate government entities, or any agency or instrumentality of the preceding entities (including any local educational agency or institution of higher education), and including legislative and judicial departments. The term does not include contractors, or grantees, of state or local governments.”
There are many benefits for state and local governments through the Cooperative Purchasing Program, however, it is not fully adopted. Many entities are unable to overcome a number of legal as well as administrative barriers to take advantage of the GSA Schedule contracts.
Since 2007, the Disaster Purchasing Program has allowed state, local and tribal governments to purchase from all GSA Schedules. These entities, like their federal counterparts, can utilize GSAAdvantage!, GSA eBuy and the GSA Reverse Auctions platform under Disaster Purchasing. The majority of GSA Contractors opt to participate in the Disaster Recovery Program.
The program features include:
Many of the small details of the Disaster/Recovery Program can be found on the GSA Disaster Purchasing FAQ page.
The “Checklist” to complete the GSA Schedule 70 (GSA IT Contract) Documents to submit can be found on the FedBizOpps website.
The process to get into the GSA Schedule / MAS program is described in detail on our What is a GSA Contract? webpage.
The full list of GSA / MAS SINs are found in the GSA eLibrary website.