Big changes are here for GSA contractors in 2026. Transactional Data Reporting (TDR) is now mandatory under Refresh 31, replacing the old Price Reduction Clause (PRC) and Commercial Sales Practices (CSP-1). This simplifies reporting but introduces stricter requirements. Contractors must accept Mass Modification A909 by May 2026 to avoid suspension. Here’s what you need to know:
Key Updates:
- Mandatory TDR: Monthly sales reporting required by all contractors starting April 1, 2026, for early adopters.
- Stricter Sales Thresholds: $100,000 in the first five years; $125,000 for each renewal period.
- Cybersecurity Overhaul: Adoption of NIST SP 800-171 Revision 3, requiring nine critical security controls and 1-hour incident reporting.
- Contract Eliminations: Over 1,600 contracts removed in FY 2025 for non-compliance, saving $24M in costs.
What You Should Do Now:
- Accept Mass Modifications: Complete by May 2026 to stay in the program.
- Update Systems: Ensure compliance with TDR and NIST SP 800-171 Rev. 3.
- Prepare for Audits: Gather documentation like payroll records and subcontractor compliance reports.
Miss the deadlines, and you risk losing access to the $51.5 billion GSA MAS market. Now’s the time to act. Contractors who meet these requirements position themselves for success in an increasingly competitive federal market.
Significant Changes for MAS Refresh 31: What You Need To Know
Major Compliance Changes for 2026
In 2026, GSA compliance is set to undergo a major transformation, with a particular focus on bolstering cybersecurity measures for contractor-handled Controlled Unclassified Information (CUI). On January 5, 2026, GSA introduced CIO-IT Security-21-112 Revision 1, outlining how contractors must secure CUI in nonfederal, contractor-owned environments. This new directive creates a distinct compliance path that differs from the Department of Defense’s approach, presenting a dual compliance challenge for contractors working across multiple agencies.
CIO-IT Security-21-112 Revision 1
This updated policy shifts the focus to securing CUI in contractor-owned systems rather than federal ones. It adopts a flexible Risk Management Framework (RMF) approach, requiring contractors to provide a Memorandum for Record (MFR) instead of pursuing a standardized certification like the Department of Defense’s CMMC.
One of the standout requirements of this policy is incident reporting within one hour – contractors must notify authorities of any suspected or confirmed cybersecurity incidents involving CUI within 60 minutes. Additionally, security assessments must be conducted by either a FedRAMP-accredited Third Party Assessment Organization (3PAO) or a GSA-approved independent assessor, with reassessments mandated every three years. Contractors are also tasked with ensuring their systems meet at least an 85% compliance level with NIST guidelines or CIS benchmarks. To further strengthen security, GSA has updated its baseline to align with NIST SP 800-171 Revision 3.
NIST SP 800-171 Revision 3 Adoption
GSA has transitioned from NIST SP 800-171 Revision 2 to Revision 3 as the foundational compliance standard for contractor systems. This marks a significant departure from the Department of Defense, which continues to rely on Revision 2 for its CMMC program.
Jacob Horne, Chief Cybersecurity Evangelist at Summit 7, explained: "GSA’s revised guidance establishes a formal process for verifying that contractors handling CUI have implemented the requirements in NIST SP 800-171 and 800-172, both Revision 3".
The new baseline includes additional security measures from NIST SP 800-172 Revision 3, specifically for high-value assets, and incorporates selected privacy controls from NIST SP 800-53 Revision 5. Contractors already compliant with Revision 2 will need to update their System Security and Privacy Plans (SSPPs) during their next annual update or three-year reauthorization cycle.
Chris Camejo, cybersecurity expert at TrustedSec, highlighted: "These revisions [NIST 800-171 Rev 2 vs Rev 3] are dissimilar enough from each other that some effort will be required to migrate a program that is already compliant with Revision 2".
The revised guidelines also introduce nine critical security controls that are mandatory for system authorization.
9 Required Security Controls
GSA has outlined nine essential controls that contractors must implement to achieve system authorization. These controls are non-negotiable, meaning no Plans of Action and Milestones (POA&Ms), compensating measures, or risk acceptance will be allowed. Key requirements include multi-factor authentication (MFA) for all accounts, encryption of CUI both at rest and in transit using FIPS 140-2 validated modules, regular vulnerability scanning, and the removal of unsupported software components.
| Requirement | Control Family | What Blocks Authorization |
|---|---|---|
| 03.01.02 | Access Control | Access enforcement not aligned with approved policies |
| 03.01.12 | Access Control | Remote access lacks usage restrictions or configuration controls |
| 03.05.03 | Identification & Authentication | MFA absent for any privileged or non-privileged account |
| 03.11.02 | Risk Assessment | Vulnerabilities not scanned at required frequency or not remediated |
| 03.13.01 | System & Communication Protection | Boundary communications unmonitored or network segmentation absent |
| 03.13.08 | System & Communication Protection | CUI transmitted or stored without cryptographic protection |
| 03.13.11 | System & Communication Protection | Cryptography not properly implemented or documented (FIPS validation) |
| 03.14.01 | System & Information Integrity | System flaws not identified/corrected; updates not installed timely |
| 03.16.02 | System & Services Acquisition | End-of-life or unsupported system components in production |
Contractors must also document the FIPS 140-2 validation certificate numbers for all cryptographic modules used to protect CUI, as this is a frequent area of non-compliance during assessments. Additionally, system boundary diagrams must clearly detail all administrative access paths, jump servers, and log aggregation infrastructure, ensuring full visibility and accountability.
The 5-Phase Compliance Process
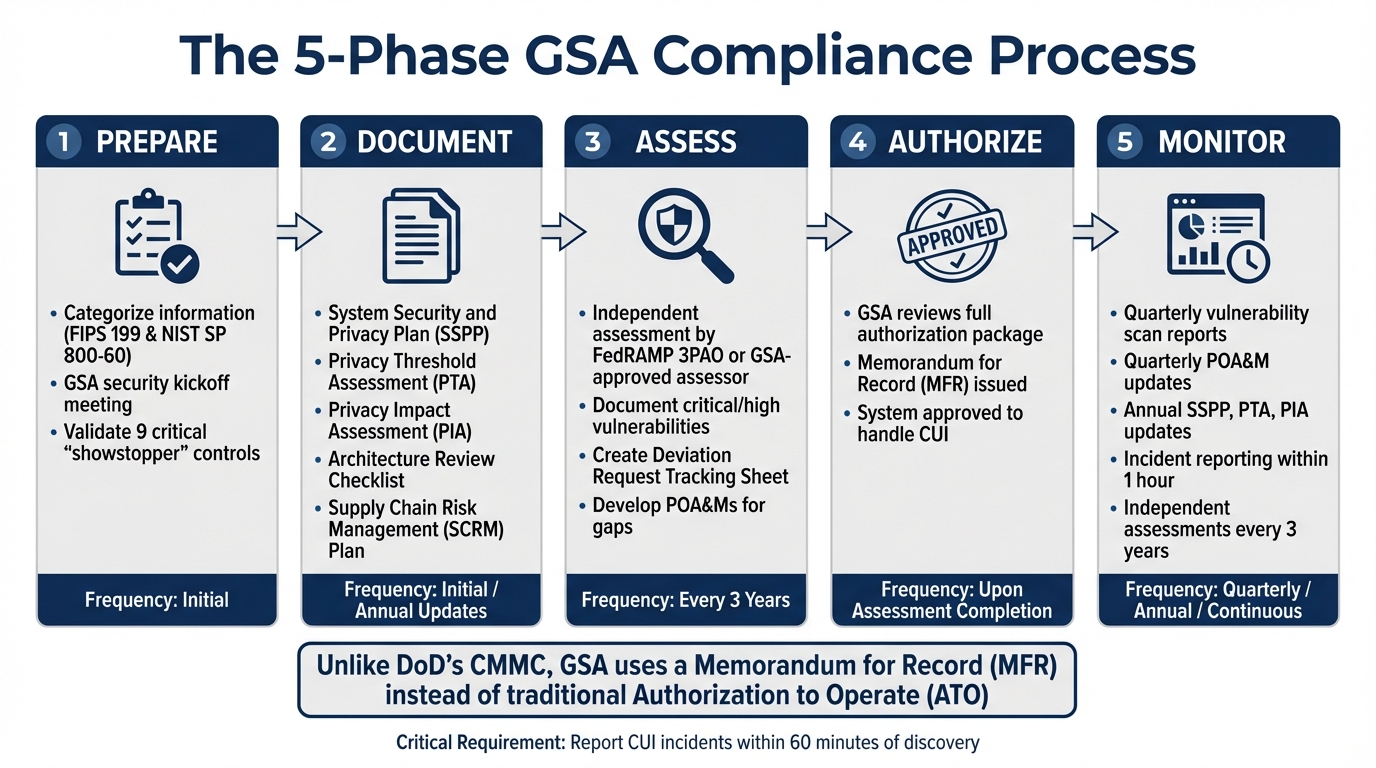
GSA 5-Phase Compliance Process for 2026
The GSA has outlined a five-phase framework to guide contractors through achieving and maintaining compliance by 2026. These phases – Prepare, Document, Assess, Authorize, and Monitor – create a clear path from initial setup to ongoing compliance. Unlike the Department of Defense’s CMMC model, the GSA uses a Memorandum for Record (MFR) instead of the traditional Authorization to Operate (ATO). This approach balances flexibility with rigorous standards. The structure aligns with the enhanced cybersecurity measures discussed earlier.
Prepare and Document
The Prepare phase requires contractors to categorize their information types based on FIPS Publication 199 and NIST SP 800-60 standards. A GSA security kickoff meeting is mandatory to validate nine critical "showstopper" controls.
Next, in the Document phase, contractors must compile a detailed submission package. This includes:
- System Security and Privacy Plan (SSPP)
- Privacy Threshold Assessment (PTA)
- Privacy Impact Assessment (PIA)
- Architecture Review Checklist
- Supply Chain Risk Management (SCRM) Plan
GSA approval of these documents is a prerequisite for moving forward. This step reinforces the heightened emphasis on security in recent compliance updates.
Once these initial steps are complete, contractors transition to evaluation and ongoing monitoring.
Assess, Authorize, and Monitor
The Assess phase involves an evaluation by a FedRAMP-accredited Third Party Assessment Organization (3PAO) or a GSA-approved assessor. Any unresolved critical or high vulnerabilities must be documented in a Deviation Request Tracking Sheet and addressed using Plans of Action and Milestones (POA&Ms).
In the Authorize phase, GSA reviews the full authorization package. Upon approval, they issue an MFR, formally recognizing the system’s readiness to handle Controlled Unclassified Information (CUI).
The final phase, Monitor, ensures continuous compliance. Contractors are required to:
- Submit quarterly vulnerability scan reports and POA&M updates.
- Update the SSPP, PTA, and PIA annually.
- Conduct independent assessments every three years.
Additionally, the incident reporting protocol is strict: any suspected or confirmed CUI incident must be reported within 60 minutes of discovery. Chris Camejo from TrustedSec highlighted the challenge of this requirement:
"Contractors must report suspected and confirmed CUI incidents within one hour of discovery… This one-hour requirement is unusually compressed and may be difficult to operationalize".
| Phase | Key Deliverables | Frequency |
|---|---|---|
| Prepare | FIPS 199 Categorization, Kickoff Meeting, Showstopper Control Check | Initial |
| Document | SSPP, PTA, PIA, Architecture Review Checklist, SCRM Plan | Initial / Annual Updates |
| Assess | Independent Assessment Report, Deviation Request Tracking Sheet, POA&Ms | Every 3 Years |
| Authorize | GSA Review, Memorandum for Record (MFR) | Upon Assessment Completion |
| Monitor | Vulnerability Scans, POA&M Updates | Quarterly / Annual |
How Updates Affect Small Businesses and Contractors
The 2026 compliance requirements bring a mix of challenges and opportunities for contractors, both established and new. Key areas like pricing transparency, cybersecurity, and program eligibility are at the forefront, reflecting the broader GSA initiative to cut costs and improve efficiency.
Requirements for Current Contractors
For those already in the game, the new rules introduce some non-negotiable tasks:
- TDR Reporting: Contractors must now submit monthly sales data within 30 days after the end of each month.
- 8(a) Program Compliance: Over 1,000 8(a) firms received suspension notices after failing to respond to a December data call. Required documents are due by February 19, 2026.
- Contract Reviews: Contracts exceeding $20 million are under scrutiny for subcontractor compliance and fair pricing. Reviews must be completed by February 28, 2026. According to Secretary Pete Hegseth, non-essential contracts will be discontinued.
To stay ahead, contractors should review their TDR systems, ensure NIST SP 800-171 cybersecurity controls are in place, and maintain proper Limitation on Subcontracting (LOS) documentation. Gathering payroll records, invoices, and other key documents now can help avoid audit issues, especially for high-value contracts.
Opportunities for New Contractors
For newcomers, the updated rules simplify some processes while setting a higher bar for compliance.
- Streamlined Entry: New contractors must adopt TDR reporting from the outset, skipping the complex Most Favored Customer disclosures. Those with pending non-TDR offers must resubmit under TDR guidelines within 10 business days of receiving GSA notification to keep their place in the review queue.
- Reduced Competition: Stricter compliance standards have led to fewer competitors. For example, only 65 new firms were accepted into the 8(a) program in 2025, compared to 2,100 under the previous administration. This creates opportunities for well-prepared businesses.
- AI-Driven Evaluations: Proposals are now reviewed using AI tools that focus on pricing accuracy, labor mapping, and performance. Contractors must avoid vague scopes and inflated pricing models to remain competitive.
To meet the $100,000 minimum sales threshold within the first five years, new contractors should focus on a "Schedule-first" marketing strategy. This means prominently displaying the MAS contract number and SINs on capability statements and targeting agencies that prefer Schedule purchases. For those working with Controlled Unclassified Information (CUI), partnering with experts like GSA Focus can help streamline document preparation and compliance with the five-phase authorization process.
| Compliance Area | Current Contractors | New Contractors |
|---|---|---|
| TDR Reporting | Accept TDR Mass Modification within 90 days and transition to monthly reporting | Mandatory from the outset |
| 8(a) Program | Respond to audit data calls by February 19, 2026 | Lower acceptance rate (65 firms in 2025) |
| Sales Threshold | $125,000 per five-year option period | $100,000 within the first five years |
| Cybersecurity | Implement NIST SP 800-171 controls | Implement NIST SP 800-171 controls |
Both existing and new contractors need to adapt quickly to these changes. Whether it’s staying compliant with evolving GSA standards or leveraging reduced competition, success will depend on agility and preparation in this tightening regulatory environment.
GSA Compliance vs. Other Federal Standards
Navigating compliance for federal contracts can be tricky, especially when juggling multiple frameworks. The GSA’s 2026 framework introduces unique challenges for contractors working across agencies, mainly because it diverges from other federal standards. One of the most notable differences lies in the NIST baseline requirements. While the GSA now mandates compliance with NIST SP 800-171 Revision 3, the Department of Defense (DoD) continues to use Revision 2 for both CMMC and DFARS 252.204-7012. This mismatch forces contractors to either manage two distinct sets of controls or maintain entirely separate environments for civilian and defense contracts.
Another key distinction is the timing of assessments. Unlike CMMC, which demands certification before a contract is awarded, the GSA framework allows for a more flexible, collaborative approach. Contractors can implement controls post-award, as long as they address the nine critical "showstopper" controls upfront. Chris Camejo from TrustedSec highlights this difference, noting that GSA works with contractors after the award, offering a level of flexibility not seen in CMMC’s pre-award certification process. Additionally, the GSA framework permits Plans of Action and Milestones (POA&Ms) for non-critical gaps, whereas CMMC 2.0 enforces stricter requirements for achieving specific maturity levels.
Incident reporting is another area where the GSA framework stands apart. The GSA requires contractors to report incidents within just one hour, a stark contrast to the 72-hour window typical for DFARS and many CMMC contracts. This accelerated timeline means contractors need to update their incident response plans, incorporating automated alerts and pre-prepared templates to meet this demanding requirement.
To provide a clearer picture, here’s a comparison of key features across these frameworks:
Framework Comparison Table
| Feature | GSA (CIO-IT Security-21-112 Rev 1) | CMMC 2.0 | DFARS 252.204-7012 |
|---|---|---|---|
| NIST Baseline | NIST SP 800-171 Rev. 3 | NIST SP 800-171 Rev. 2 | NIST SP 800-171 Rev. 2 |
| Assessment Timing | Post-award (with showstopper implementation) | Pre-award (Certification required) | Self-assessment / Post-award |
| Incident Reporting | 1 Hour | Varies by contract | 72 Hours |
| Assessment Type | GSA-approved Independent Assessor / 3PAO | C3PAO (Level 2/3) or Self (Level 1) | Self-assessment (typically) |
| Lifecycle Phases | 5 Phases (Prepare, Document, Assess, Authorize, Monitor) | Maturity Levels (1-3) | Continuous Compliance |
| POA&M Allowance | Allowed (except for 9 showstoppers) | Limited / Restricted | Allowed |
Akin Gump Strauss Hauer & Feld LLP underscores the impact of these differences, stating:
"GSA’s Guide is the first major framework to require contractors to implement NIST SP 800-171 Revision 3 (Rev. 3)… even contractors that have prepared for CMMC compliance will need to revisit their controls."
For contractors working with both GSA and DoD, conducting a detailed gap analysis between Revision 2 and Revision 3 is essential. This step ensures internal controls align with both frameworks and helps avoid potential compliance conflicts. Adapting to these divergent standards requires a well-thought-out strategy to maintain seamless operations across federal contracts.
Conclusion
The 2026 GSA compliance landscape is set to redefine federal contracting. With the mandatory shift to Transactional Data Reporting (TDR) under Refresh 31, the GSA Schedule program is undergoing one of its most transformative updates in decades. For small businesses, this change presents both hurdles and opportunities – reducing administrative complexity while raising expectations for accountability and performance.
The numbers speak volumes: over $60 billion in contract savings and the removal of 1,600 underperforming contracts in Fiscal Year 2025 alone. With full TDR implementation, annual cost avoidance is expected to reach approximately $50 million. Additionally, removing 36 outdated clauses could save contractors between $500 million and $1 billion in compliance costs each year. These changes highlight the urgency of the steps businesses need to take.
For small businesses, quick action is critical. Contractors must accept Mass Modifications within 90 days of issuance. Non-TDR proposals currently in progress should be withdrawn and resubmitted to meet the new requirements. Internal systems also need to be updated to support monthly transactional reporting, which must be completed within 30 days after the end of each month. As B2G Connect aptly puts it, "2025 is the strategic window. 2026 is the reaction window".
Navigating these changes successfully requires expert support. GSA Focus offers a full-service solution tailored to small businesses, covering every aspect of GSA Schedule management – from document preparation to compliance assurance and negotiation support. Their streamlined approach minimizes time investment while opening doors to the $52 billion GSA MAS program.
The enhanced compliance framework sets the stage for a thriving procurement cycle. Small businesses that adapt proactively – by refining pricing models, ensuring defensible practices, and demonstrating clear capabilities – will position themselves for success in 2026 and beyond.
FAQs
What data do I need to collect to comply with mandatory TDR?
To meet the mandatory TDR requirements, you need to collect 16 specific transaction-level data points for every sale. This information must be submitted monthly via the FAS Sales Reporting Portal, and the deadline is within 30 days after the end of each month. To stay accurate and compliant, consider automating your data collection process – it can save time and reduce errors.
How do I prepare to meet the 1-hour CUI incident reporting rule?
To meet the 1-hour reporting requirement for Controlled Unclassified Information (CUI), it’s essential to have a well-defined incident response process in place. Start by documenting clear procedures that outline every step of the response. Train your team to recognize potential incidents quickly and accurately, ensuring they understand the urgency of reporting.
Additionally, configure your systems to send immediate alerts when suspicious activity is detected. This allows your team to act swiftly – detecting, analyzing, and responding to incidents within the critical one-hour window. Throughout the process, maintain detailed records of every action taken. This documentation is crucial for compliance with both GSA and DHS standards.
What’s the fastest way to close the gap from NIST 800-171 Rev. 2 to Rev. 3?
To efficiently shift from NIST 800-171 Rev. 2 to Rev. 3, treat the process like a project management initiative. Prioritize migrating controls, drafting a comprehensive Supply Chain Risk Management (SCRM) Plan, and integrating the necessary practices. This method streamlines the transition while maintaining compliance with the updated requirements.
Related Blog Posts
- Top 5 Compliance Issues in GSA Contracts
- Ultimate Guide to GSA Compliance Standards
- Regulatory Requirements for Federal Contracts
- GSA Reporting Deadlines: Ultimate Guide